via IFTTT
The Pauline Corpus and the Reality of Pseudepigraphy
Ancient religious texts are not divinely delivered documents but physical artifacts constructed to address immediate human concerns. Within the 13 letters attributed to the Apostle Paul, modern scholarship identifies a significant divide: seven “undisputed” letters universally accepted as authentic, and six Deutero-Pauline epistles (Ephesians, Colossians, 2 Thessalonians, 1 and 2 Timothy, and Titus).
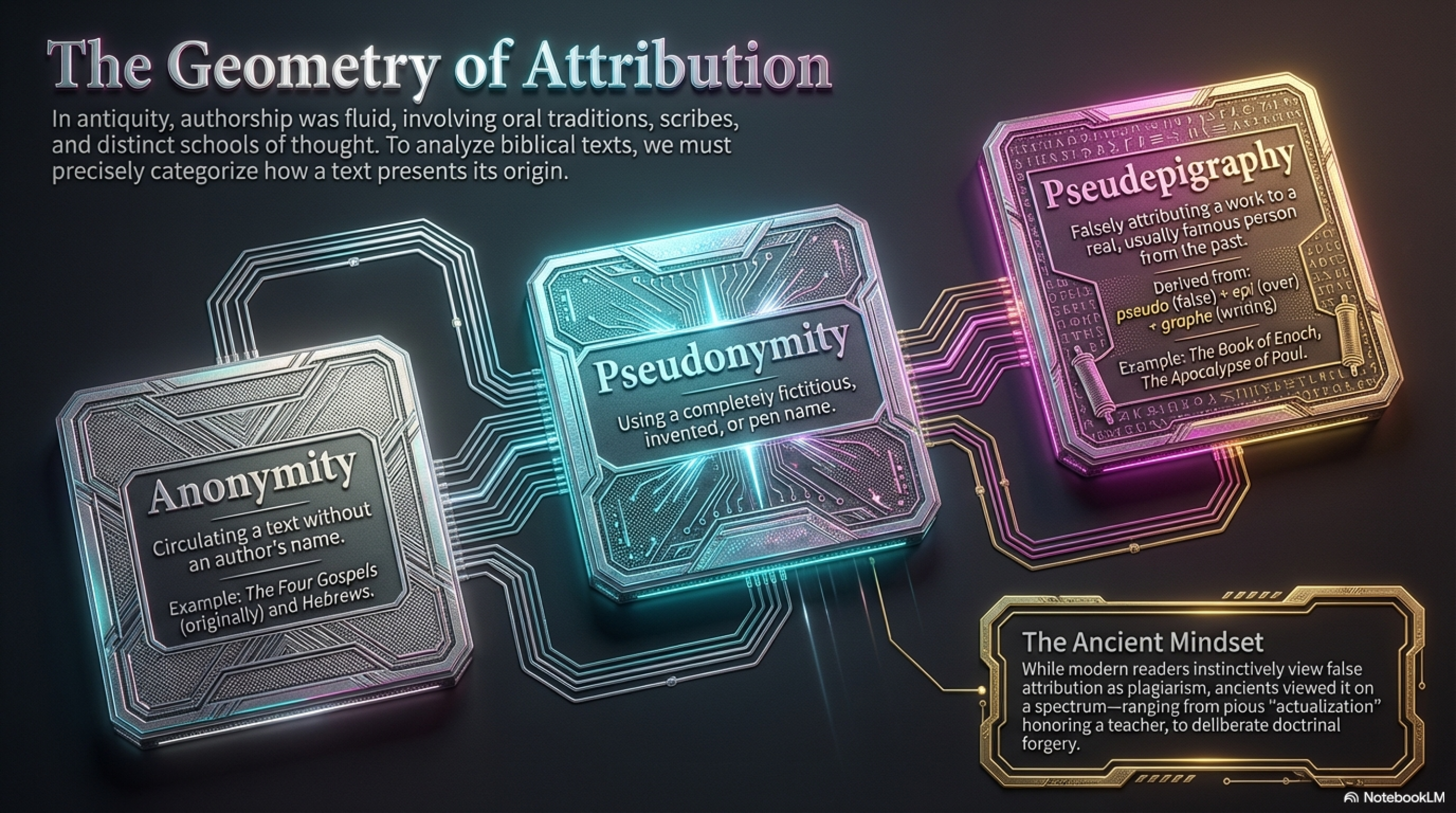
Biblical scholars classify these six works as pseudepigrapha—falsely attributed works written by anonymous authors who actively assumed Paul’s identity decades after his death. This means nearly half of the Pauline corpus relies on intentional identity deception to assert theological authority.
Debunking the “Innocent Tribute” Theory
A common defense, known as the “philosophical school theory,” suggests these texts were innocent tributes written by disciples to honor their master. However, historical evidence contradicts this “benign forger” assumption. Early Christian communities prioritized authenticity over orthodoxy and maintained a strict intolerance for forgeries.
The theologian Tertullian, for example, recorded that an Asian presbyter was immediately deposed after being caught publishing a text under Paul’s name. If a letter was exposed as a pseudepigraph, it was categorically excluded from the liturgy, regardless of its theological merit. Consequently, these authors were not writing innocent tributes; they were engaging in high-stakes, calculated deceptive interventions.
Rhetorical Engineering: The Case of Ephesians
To bypass community detection, anonymous authors deployed advanced “rhetorical engineering”. The Letter to the Ephesians serves as a primary case study. In Chapter 3, the text breaks its pastoral flow for an autobiographical digression regarding the author’s divine commission.
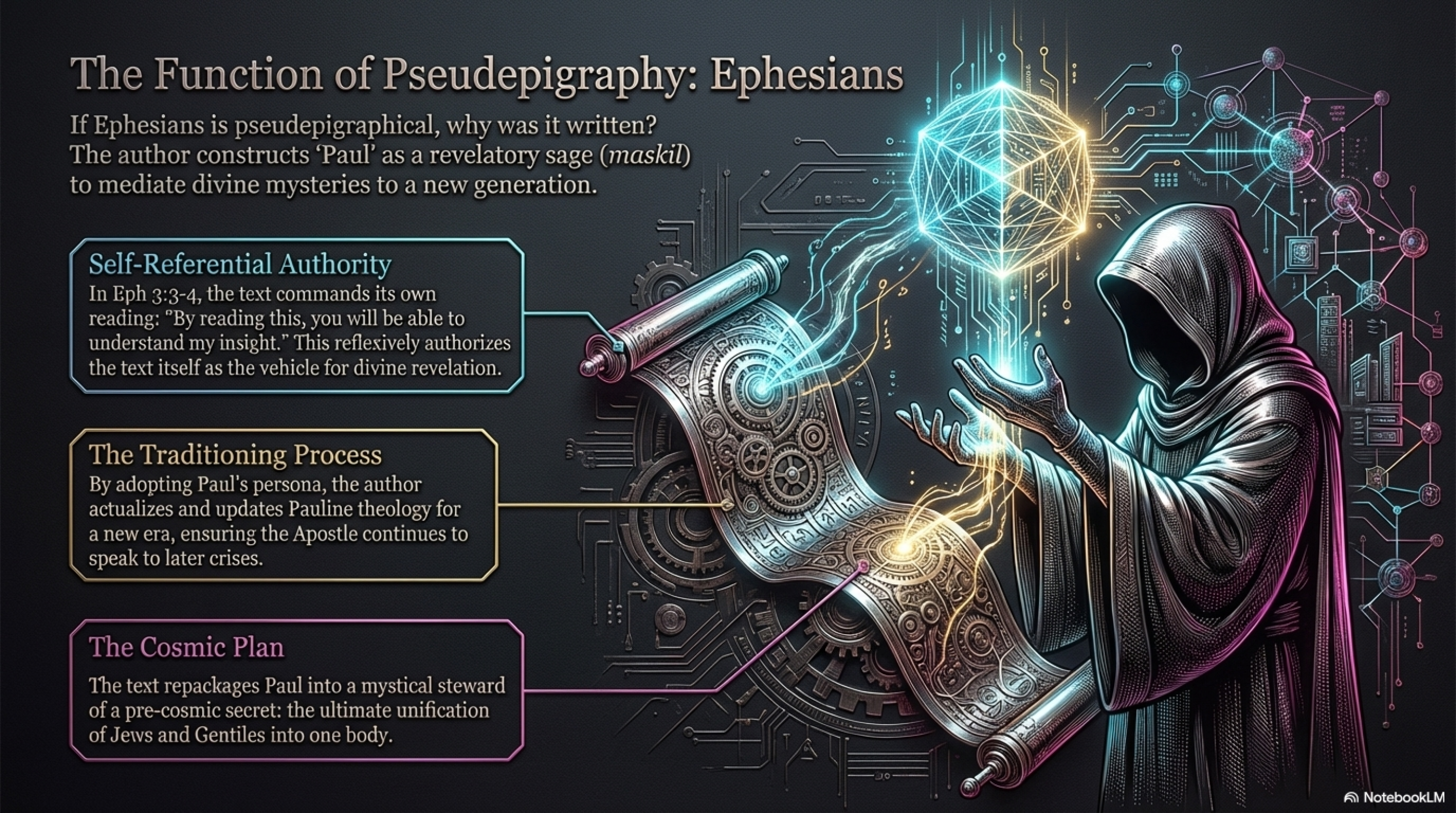
The author of Ephesians utilizes a self-referential loop to validate the text:
- Textual Meta-Reference: The author explicitly connects his act of writing to the audience’s act of reading.
- Internal Verification: The text dictates that the act of reading this specific document is the only mechanism required to verify the author’s insight.
- Closed System: The constructed author validates the text, and the reader validates the author by accepting the “insight” provided within the text itself.
By shifting the locus of authority from Paul’s historical actions (as a tent-maker and church planter) to a “textualized visionary,” the author replaced the dead apostle with an immortal, cosmic mediator.
Jewish Literary Precedents: The Qumran Model
The strategy used in Ephesians did not emerge in a vacuum; it drew upon sophisticated Jewish literary technologies found in the Dead Sea Scrolls.
- The Pesharim: These commentaries on prophetic texts (like Habakkuk) frame ancient words as coded mysteries. They establish a mediator, such as the “Teacher of Righteousness,” as the only person capable of identifying the true intent of the text.
- The Hodayot: These hymns focus on a “constructed eye”—a mediator of knowledge appointed to test the community through “wonderful mysteries”.
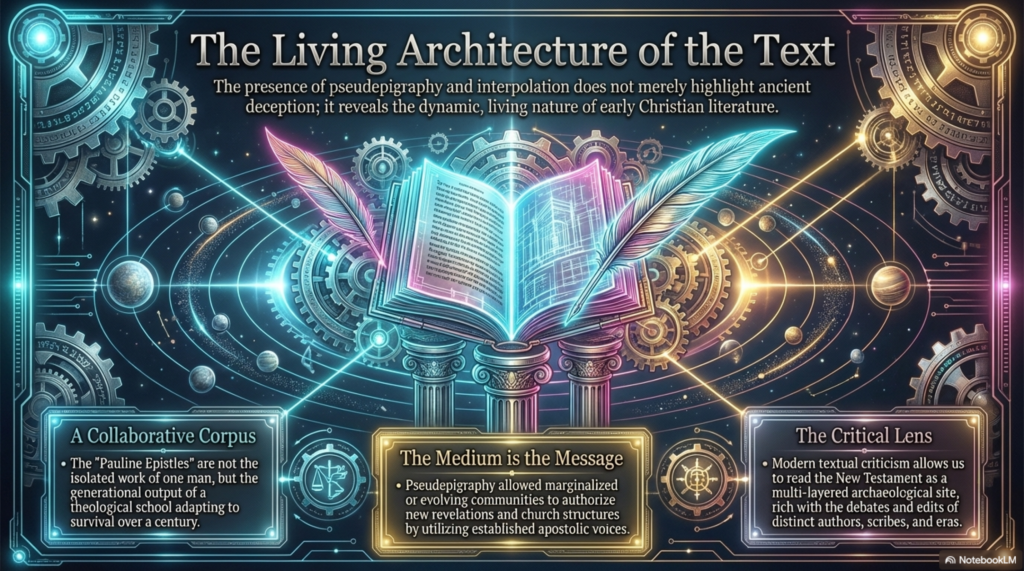
Both the Qumran texts and the Deutero-Pauline letters establish the written document as an ongoing revelatory site accessible only through a textualized visionary.
The Anatomy of a Pseudepigraph: A Replicable Pipeline
The mechanics of scriptural forgery can be consolidated into a five-step “pipeline” that allowed anonymous authors to exert influence over the early church:
- Historical Crisis: A catalyst, such as shifting community rules or the delay of the Parousia, creates an authority vacuum.
- The Vacuum: The community requires absolute theological direction to survive instability.
- Pseudonymous Authorship: Anonymous authors step into the vacuum by assuming a dead apostle’s identity.
- Self-Referential Authorization: The author instructs the reader to accept the document itself as proof of its own validity.
- Textualized Revelation: The final output is a self-contained site of divine truth that dictates the boundaries of the canon.
In conclusion, pseudepigraphy was not a matter of innocent false attribution but a deliberate rhetorical technology designed to engineer divine authority and permanently shape Christian theology.